Lithuania: Hotspot for SMTP and legacy protocol abuse
Recent telemetry from the SikkerNet honeypot network shows an unusual protocol distribution targeting our Lithuanian sensor. Unlike most regions, where SSH brute-force attempts dominate, Lithuania is currently receiving a disproportionate volume of traffic focused on legacy and service-specific protocols.
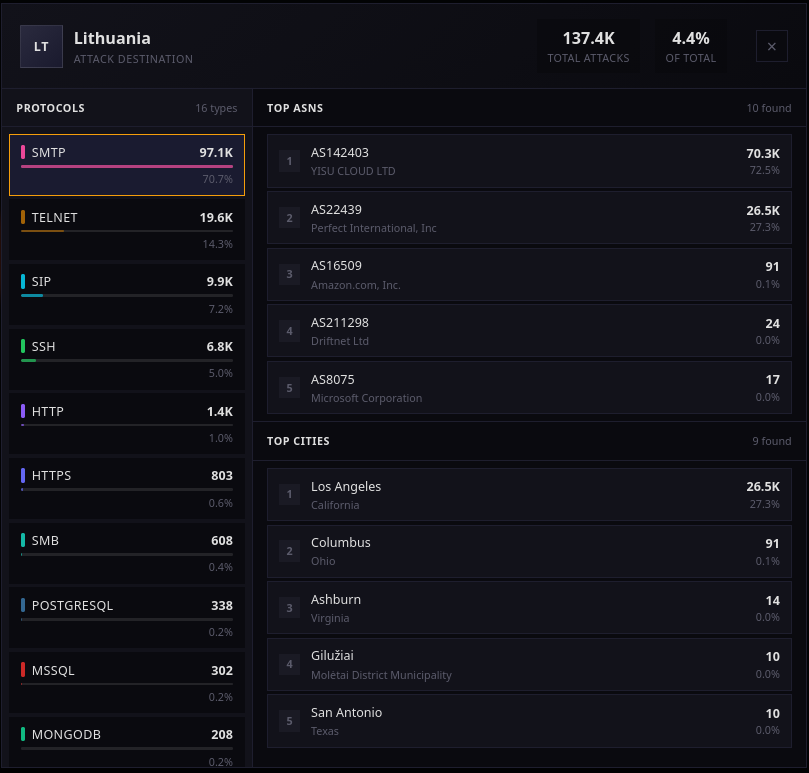
SMTP alone accounts for over 70% of observed attacks against this sensor, followed by Telnet and SIP. SSH, which is typically the primary target across other locations in our network, represents only a small fraction of the activity here.
Protocol Distribution
The Lithuanian deployment shows a clear deviation from global patterns:
- SMTP is the dominant attack vector, suggesting automated abuse campaigns targeting mail infrastructure.
- Telnet and SIP activity indicates opportunistic scanning against older or historically vulnerable services.
- SSH traffic exists but is significantly lower compared to other regions.
This shift toward legacy protocols often correlates with botnet behavior, mass exploitation attempts, or infrastructure testing rather than traditional credential brute-forcing.
Attacker Origin
Analysis of source ASNs and cities indicates that most activity originates from large cloud providers rather than local Lithuanian networks. High-volume sources include ASNs associated with VPS and hosting platforms, reinforcing the likelihood of automated campaigns rather than targeted attacks.
The presence of cities such as Los Angeles and Columbus among top origins highlights how geographically distributed infrastructure is being used to target a single regional sensor.
What This Suggests
While individual sensors commonly reflect global noise patterns, this dataset suggests localized campaign behavior or routing bias toward the Lithuanian node. Possible explanations include:
- Automated SMTP abuse waves using cloud infrastructure
- Opportunistic scans targeting legacy protocols
- Network placement making the sensor more visible to specific scanning clusters
Closing Thoughts
One of the advantages of running geographically distributed high-interaction sensors is the ability to observe how attack patterns differ between regions. Lithuania currently stands out as an example where SMTP abuse significantly outweighs more common vectors like SSH, offering useful insight into evolving attacker priorities.
Comments
No comments yet. Be the first to share your thoughts!